Deepfactor 2.2 enhancements include support for BYO-Certificates, detailed Python stack traces, and robust injection of Deepfactor runtime observability!
Given the fast-paced nature of development at a software startup, it’s always important to pause – take a deeeeep breath – and 1) acknowledge your many accomplishments … and 2) recognize where “growing pains” might be preventing maximum and ongoing success. This is especially true with security software where stability, operational simplicity, and accuracy are of the utmost importance for protecting customers’ applications!
With the release of Deepfactor 2.2, our goal is to be hyper-focused on deploying a seamless developer experience for observing cloud native applications running in Kubernetes. From providing Helm Charts to ease the installation of our portal and mutating webhook, to ensuring our instrumentation performs robust compatibility checks, to adding stack trace support for Python, our efforts are concentrated on reducing operational overhead, simplifying the user experience, and maximizing time to value! Each new feature, and every minor refinement, aimed to improve the end-to-end experience for your developers.
Continue reading after the matrix to learn more about the latest version of Deepfactor!
| Features | Enhancements | |
| Core Platform |
|
|
| Insights |
|
|
| Integrations |
|
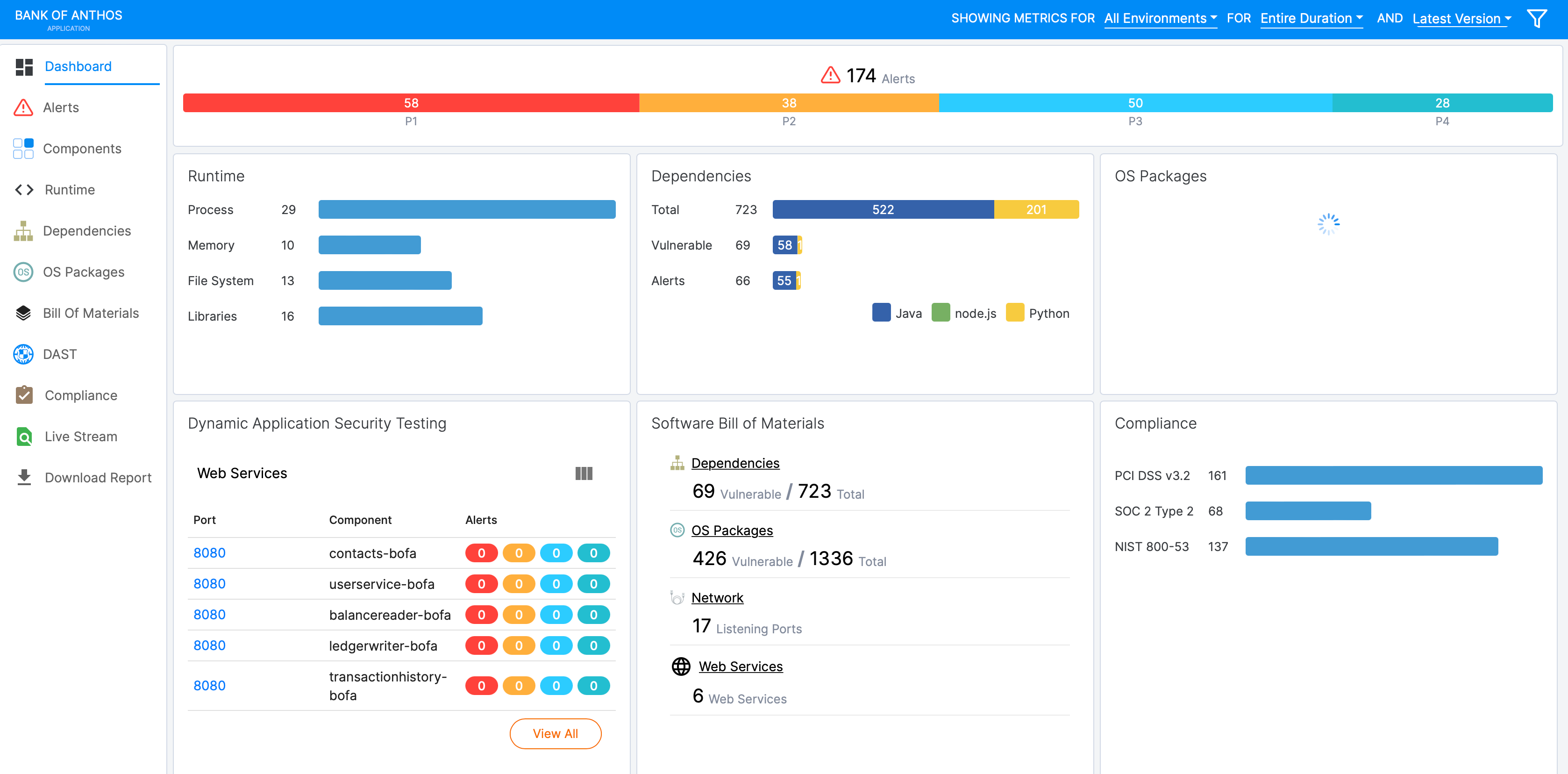
Streamlined UX Enhancements – New Dashboards!
Improved Instrumentation
With our latest release, our mutating webhook received some major updates to ensure near zero-touch instrumentation of customer applications. Without requiring intrusive agents or privileged sidecars, our mutating webhook can automatically insert a language-agnostic library into Kubernetes applications to observe every thread, process, container, and pod. And with our latest changes, our mutating webhook supports:
- Robust pre-flight checks ensure the successful deployment of the application regardless of instrumentation status
- Mixed containers running processes linked with different types of libc
- Automatic configuration of the necessary environment variables (i.e. setting of LD_PRELOAD) based on the container’s entrypoint
In addition, we’re excited to announce the Tech Preview of Namespace Instrumentation which can instrument pods in a namespace with and without pod annotations. This can be enabled per namespace configured in the webhook override.yaml config or per pod based on annotations.
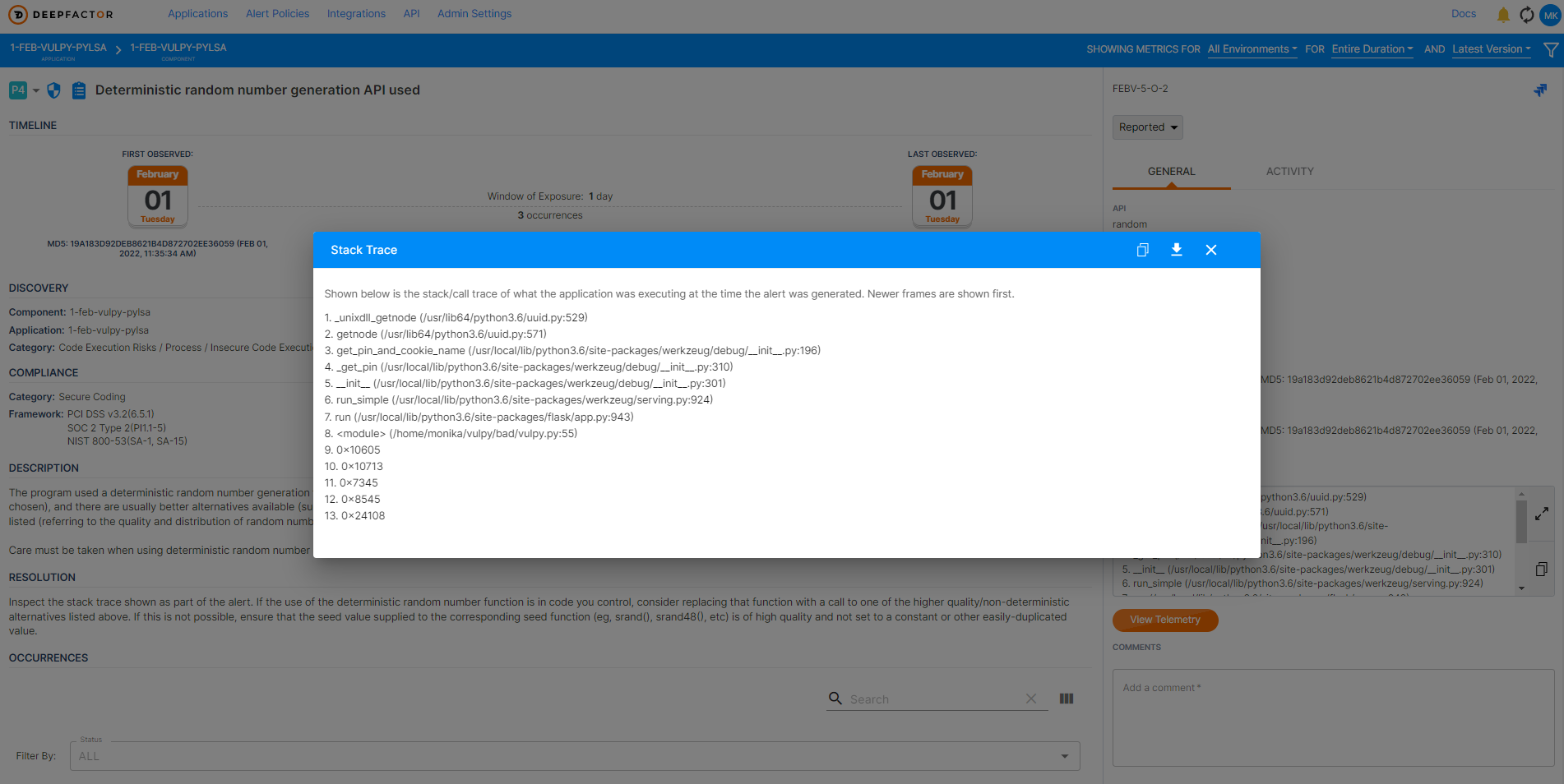
Python Language Specific Agent
Deepfactor provides a Python LSA that can be used to deliver stack trace information for many alerts displayed in the Deepfactor Portal. This agent can be injected by passing the “-l python” option to the dfctl run command.
Example: dfctl run -a "my application" -c "my component" --version "111" -v -l "python" --cmd python3 myapp.py
Visit our Release Notes for more information about our latest releases. And, as always, for those interested in learning more about Deepfactor and the improvements introduced in v2.2, you can request a demo.
Deepfactor is a developer security platform that enables engineering teams to quickly discover and resolve security vulnerabilities, supply chain risks, and compliance violations early in development and testing. Requiring no code changes, the Deepfactor runtime observability technology seamlessly plugs into cloud native architectures, enabling developers to identify, prioritize, and remediate application risks. The platform integrates into developers’ existing toolchains to deliver application-aware security insights with detailed information about application behavior, system calls, and stack traces that help pinpoint vulnerable code. Deepfactor simplifies and accelerates DevSecOps by empowering engineering teams to develop secure and compliant cloud native applications.