Introduction
If you are an individual using Linux or one who has been a fan of Looney Tunes/Toons then do read further to find out how Looney Toons is a step away from taking down your Linux-based application and how Deepfactor helps you identify and prevent such exploits.
What is the glibc dynamic loader?
The GNU C Library, commonly known as glibc, comprises standard C library functions which serve as an interface for system calls related to file I/O, string manipulation, memory allocation, etc. in the Linux kernel. The dynamic loader ensures availability of all the shared libraries that the application requires and links them to the executable at runtime.
What is the use of the GLIBC_TUNABLES environment variable?
Tunables is a glibc feature that provides the capability of manipulating the runtime library behavior related to memory allocation, dynamic linking, hardware capabilities, etc., primarily using an environment variable GLIBC_TUNABLES. It expects : separated name=value pairs (<tunable1>=<val1>:<tunable2>:<val2>…) where name is a predefined/custom attribute which follows the format <top namespace>.<tunable namespace>.<tunable name>
Example:
glibc.malloc.mmap_max can be used to manipulate the maximum number of chunks that can be allocated using mmap
Default value: 65536
CVE-2023-4911 (Looney Tunables)?
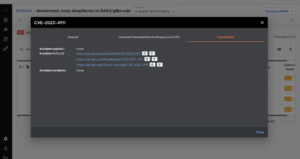
A new vulnerability (CVE-2023-4911) was recently identified by the Qualys Threat Research Unit associated with the glibc dynamic loader processing logic of the GLIBC_TUNABLES environment variable.
The buffer overflow vulnerability exists in the workflow where the dynamic loader parses the GLIBC_TUNABLES environment variable value and overrides the runtime library behavior. The parser typically trims dangerous SXID_ERASE security-level runtime library manipulations and only accepts SXID_IGNORE/NONE security level tunables. It goes for a toss though if the value of the environment variables does not follow the expected semantics.
Example: <tunable1>=<tunable2>=AAA
Assuming both tunable1 and tunable 2 have a security level SXID_ERASE, they should ideally be trimmed and no overriding of the runtime library behavior should take place. The bug instead results in a buffer overflow while parsing such values, giving an opportunity to hackers to eventually acquire root privileges, crash applications, and execute remote code.
Default installations of Fedora 37/38, Ubuntu 22.04/23.04, and Debian 12/13 are susceptible to this vulnerability but other Linux distributions could be potentially exploited as well. Alpine Linux remains an exception due to its use of musl libc instead of glibc.
Technical Details: https://www.qualys.com/2023/10/03/cve-2023-4911/looney-tunables-local-privilege-escalation-glibc-ld-so.txt
Is there a fix available?
The glibc library has been fixed for some of the linux distributions/versions as highlighted in:
- https://security-tracker.debian.org/tracker/CVE-2023-4911
- https://ubuntu.com/security/CVE-2023-4911
- https://access.redhat.com/security/cve/cve-2023-4911
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/4DBUQRRPB47TC3NJOUIBVWUGFHBJAFDL/
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/NDAQWHTSVOCOZ5K6KPIWKRT3JX4RTZUR/
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/DFG4P76UHHZEWQ26FWBXG76N2QLKKPZA/
An upgrade is necessary to patch the vulnerability.
How does Deepfactor help in identifying and preventing such issues?
Some of the questions that should be answered to tackle such issues include:
1) Is my application built on top of a vulnerable OS distribution?
Deepfactor can help identify the OS distribution associated with the application through the SCA scan and runtime monitoring capabilities.
2) Is my application composed of the vulnerable version of a package i.e is the package part of the SBOM (Software Bill Of Materials)? Are there exploits available in the wild for the identified vulnerability? Is a fix available?
Deepfactor SCA scans enable users to scan artifacts and in turn:
- Generate an SBOM
- Gather vulnerability insights i.e vulnerability metadata including CVSS scores, fix versions, exploitability information, upgrade recommendations
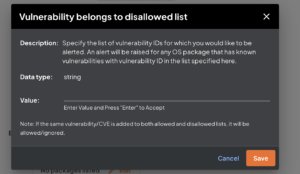
- Configure policy rules to detect and generate alerts in case of violations
3) Is my application using the vulnerable package at runtime? Is it being loaded into the memory and executed?
Deepfactor runtime instrumentation for container, non-container and Kubernetes workloads monitors applications at runtime. It highlights instances of packages being loaded and executed along with a bunch of useful security insights.
The runtime and SCA correlation capabilities help us answer the question related to what the application is composed of and what is actually being used, which in turn simplifies vulnerability prioritization.
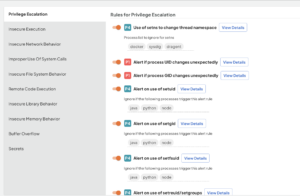
4) Does the application include a process running with elevated privileges? Does the application use buffer overflow APIs? Is there an occurrence of a remote code execution?
Deepfactor runtime security insights, along with the ability to use predefined and custom policies, enables it to detect such issues.
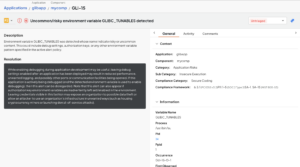
5) Are there instances of unexpected environment variable manipulation at runtime which suggest potential exploit attempts?
Deepfactor’s runtime security insights, along with the ability to use predefined and custom policies, enables it to detect such issues.
Deepfactor can help answer these and many other related questions. Deepfactor is a new approach to AppSec that combines SBOM, software composition analysis, container scans, and container runtime security into a powerful integrated platform.
Frequently Asked Questions
1. What is the CVE-2023-4911 vulnerability related to GLIBC_TUNABLES, and which Linux distributions are affected by it?
Answer: CVE-2023-4911, also known as Looney Tunables, is a vulnerability associated with the glibc dynamic loader’s processing of the GLIBC_TUNABLES environment variable. Default installations of Fedora 37/38, Ubuntu 22.04/23.04, and Debian 12/13 are susceptible to this vulnerability. For more technical details, you can refer to this link.
2. How does Deepfactor help in identifying and preventing issues like CVE-2023-4911?
Answer: Deepfactor offers several capabilities to identify and prevent vulnerabilities like CVE-2023-4911: It helps identify the OS distribution associated with the application through SCA scans and runtime monitoring. Deepfactor’s SCA scans generate an SBOM (Software Bill Of Materials) and provide vulnerability insights, including CVSS scores, fix versions, and exploitability information. Deepfactor’s runtime instrumentation monitors applications at runtime, highlighting instances of vulnerable packages being loaded and executed. Deepfactor’s runtime security insights and policy rules can detect issues like processes running with elevated privileges, buffer overflow APIs, remote code execution, and unexpected environment variable manipulations.
3. What distinguishes Deepfactor from traditional AppSec approaches, and how does it integrate various security functionalities?
Answer: Deepfactor offers a new approach to AppSec by combining SBOM, software composition analysis, container scans, and container runtime security into an integrated platform. Unlike traditional approaches, Deepfactor provides comprehensive visibility into both the composition of applications and their runtime behavior, enabling efficient vulnerability prioritization and prevention.
Free Trial Signup
The Deepfactor trial includes the full functionality of the Deepfactor platform, hosted in a multi-tenant environment.
Sign Up Today! >