Deepfactor Release 3.3 Overview
In Release 3.3 of Deepfactor Developer Security, we have made significant enhancements to the platform’s artifact scanner and runtime correlation to help users prioritize SCA findings. Users can now export the scan results in multiple formats including SPDX, as well as gate builds using exit code. We have also launched our cloud SaaS platform— users can now easily sign up for, and get value from, Deepfactor within minutes.
For additional details on 3.3 release, please review the Release Notes in Deepfactor Docs.
Release 3.3 Highlights
| Features | Enhancements | |
| Core Platform | · Multi-tenant Cloud SaaS platform. | · Improved user management capabilities such as change user role, delete user and revoke user tokens.
· Improved authentication/authorization mechanism to access Deepfactor APIs |
| Core Runtime | · Support for Oracle Linux version 8.5
· Support for Rocky Linux · Support for K8s version 1.24, 1.25, 1.26 and 1.27 · Reporting of stack traces for application using Python version 3.11 |
|
| SBOM, SCA & Container Scans | · Added SPDX report format support
· Configurable exit code, which can be used to gate builds in CI/CD pipeline · Exploits-in-the-wild information for vulnerabilities as another metric for prioritization · Classification of transitive and direct dependencies along with root dependency information |
|
| Runtime SCA | · Runtime usage of Python and NodeJS dependencies to prioritize SCA findings | |
| Runtime Security | · Added multiple runtime security alerts that look for anomalous behavior. |
Release 3.3 Details: Key Features Added
- Multi-tenant Cloud SaaS platform: We launched our multi-tenant cloud SaaS platform making it very easy for users to signup and experience the capabilities Deepfactor offers. Users can sign up for a free trial here.
- SPDX support: Users can now export their SBOM in SPDX format from the CLI as well as API and UI. We also now allow users to generate multiple reports in different formats for a single scan.
- Gate builds: dfctl scan now return a configurable exit code if the scan output results in at least one policy violation. Users can specify thresholds for CVSS score and vendor severity. They can also specify a list of disallowed license regexes to get alerted if a dependency with an undesired license is added.
- Exploit information: Deepfactor now pulls exploit information from different sources such as exploit-db, CyberSecurity Infrastructure and Security Agency (CISA) and PoCs in Github and shows it for the vulnerabilities associated with the user’s applications. This serves as another metric users can utilize to prioritize which vulnerabilities to address first.
- Runtime usage of Node.js and python applications: Deepfactor helps developers and AppSec teams prioritize which vulnerable dependencies to fix first by providing runtime usage information of dependencies. In this release, we have now extended that support to Node.js and python applications.
- Classification of transitive and direct dependencies: Modern software applications have complex SBOMs with several direct dependencies (included by your developers) importing further dependencies and those dependencies bringing more dependencies resulting in a n-depth tree. If a sub-dependency is vulnerable, developers can’t directly update them. They need to know which direct dependency is responsible for bringing in the vulnerable sub dependency so they can upgrade the direct dependency. Deepfactor not only identifies which dependencies are transitive but also the direct dependency which brought in the sub dependency.
Frequently Asked Questions
1. What are the key highlights of Deepfactor Release 3.3?
Answer: Deepfactor Release 3.3 introduces several enhancements aimed at improving artifact scanning and runtime correlation to assist users in prioritizing SCA findings. These enhancements include the launch of a multi-tenant Cloud SaaS platform, support for exporting scan results in SPDX format, the ability to gate builds using exit code, and the addition of exploits-in-the-wild information for vulnerabilities.
2. How does Deepfactor’s multi-tenant Cloud SaaS platform benefit users?
Answer: The multi-tenant Cloud SaaS platform offers users a convenient and accessible way to sign up for Deepfactor and quickly access its capabilities. Users can easily register for a free trial and experience the features Deepfactor has to offer without the need for complex setup processes.
3. What is SPDX support, and how does it enhance Deepfactor’s capabilities?
Answer: SPDX support allows users to export their SBOM (Software Bill Of Materials) in SPDX format directly from the Deepfactor platform. This feature provides flexibility by enabling users to generate multiple reports in different formats for a single scan, facilitating easier integration with existing toolchains and processes.
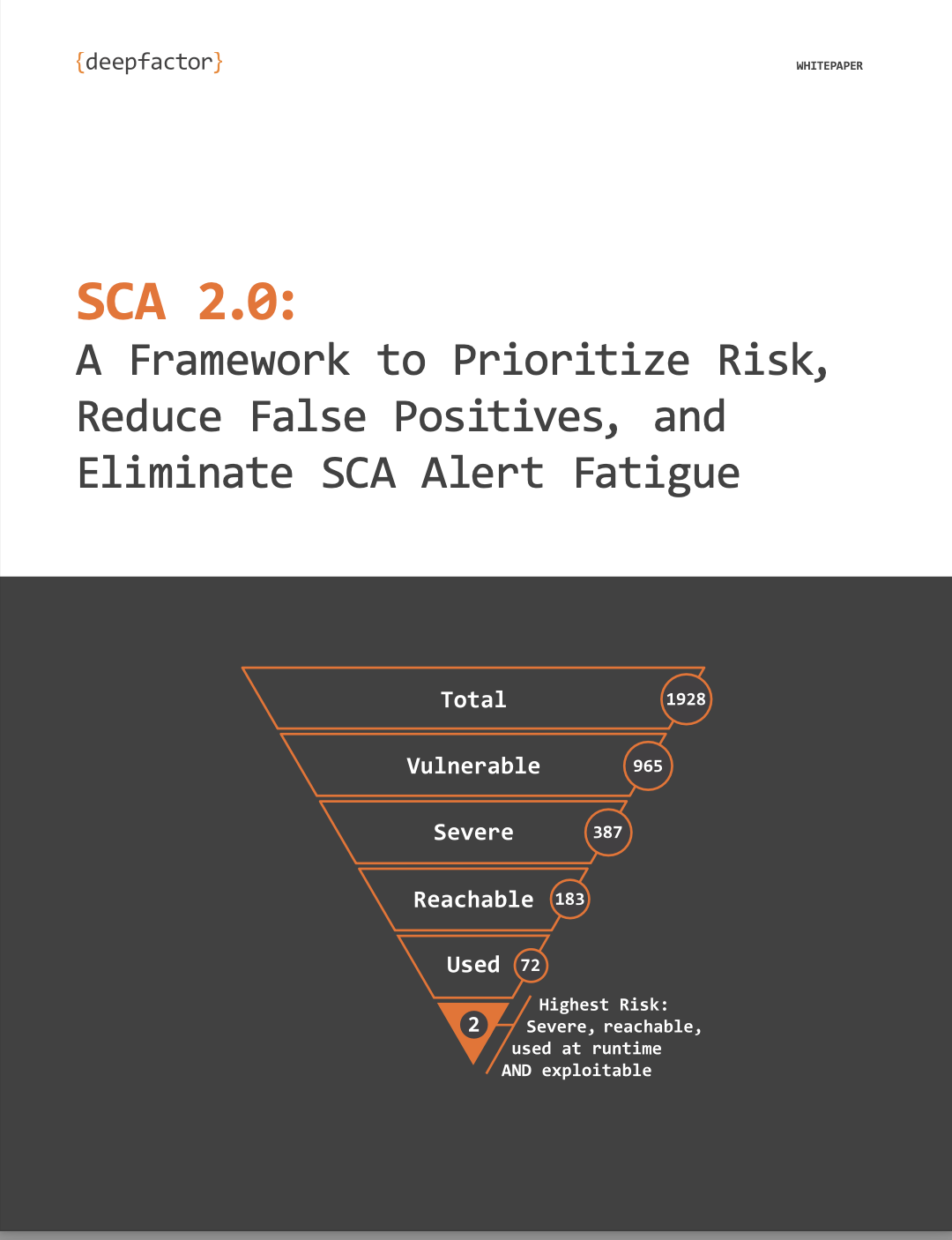
4. How does Deepfactor help users prioritize vulnerabilities in their applications?
Answer: Deepfactor introduces several mechanisms to assist users in prioritizing vulnerabilities. These include the ability to gate builds based on configurable exit codes, the provision of exploit information sourced from various platforms, and the classification of transitive and direct dependencies to identify the root cause of vulnerabilities more effectively.
Free Trial Signup
Deepfactor SaaS includes the full functionality of the Deepfactor Developer Security platform hosted in a multi-tenant environment.