In the past couple of years in my technical product role here at Deepfactor, I have had several meetings with VPs and directors of security from large, global organizations in retail, healthcare, telecom and tech. A common theme has emerged from these conversations—most organizations believe in the benefits of a DevSecOps program but are facing challenges in implementing it in their organizations. Given the unique characteristics of cloud native applications, including increased complexity and release velocity, the integration of security into the development pipeline continues to challenge engineering teams. And, unsurprisingly, the challenges are similar across organizations.
The Five Most Common Challenges to Implementing DevSecOps
I’ve summarized the common challenges organizations are facing into five categories and explore ways to overcome them.
- Challenge: Developers are taught to build products. They are not taught to build them securely.
Solution: Select and train developer security ‘Champions’ within each team who can drive DevSecOps. Motivate developers/security team members by giving them opportunities to participate in and present at key events within and outside the organization. Reward team members that are instrumental in promoting a security-conscious developer mindset. - Challenge: Lack of accountability/tracking
Solution: Integrate security tools into each step of a secure software development lifecycle (SDLC). These tools can provide metrics such as number of issues created/resolved so that each developer’s productivity in triaging and fixing security issues can be measured. - Challenge: Lack of defined processes
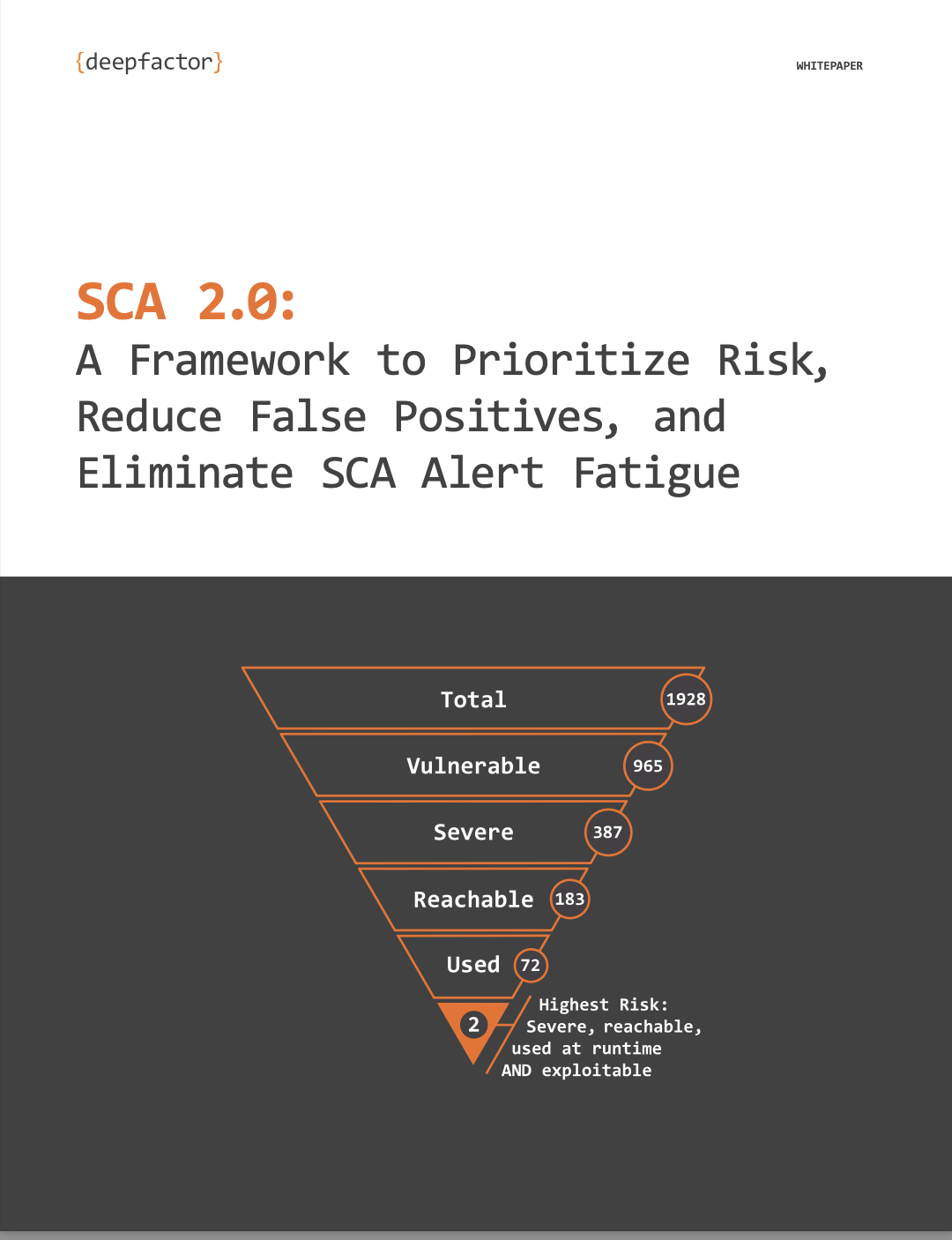
Solution: Provide DevOps templates (pipelines, base images, etc.) for teams to use. - Challenge: Developers suffer from “alert fatigue” due to large number of false positives—a “problem of plenty”
Solution: Leverage persona-based dashboards to help cut through the noise, as well as observe the running application to provide developers with contextual, application-aware information. This can include usage information, stack traces, and comprehensive insights spanning application code, dependencies, container images, and web interfaces. The identification and correlation of vulnerabilities and insecure code across application components can support engineering teams in preventing alert fatigue by helping developers discover, prioritize, and remediate the most critical security risks. - Challenge: Implementing traditional AppSec tools creates overhead and friction for developers
Solution: Traditional AppSec tools typically focus on delivering feedback via time-consuming “gates” or checkpoints, resulting in a cumbersome process for developers to create secure code. IDE and CI/CD integrations are key to encourage developers to use security tools. Emphasize technology and support systems that integrate directly into existing CI/CD workflows and toolchains.
Developer Security Platform Evaluation Criteria to Help Address These Challenges
To provide many of these solution ideas, consider a developer security platform such as Deepfactor. Developer security platforms are designed specifically to identify critical security risks early in the software development lifecycle, minimizing the time, effort, and—most importantly—impact of vulnerable and insecure applications being released into production. To help determine the right developer security option for your organization, I suggest you read the Top 5 Evaluation Criteria for Developer Security Tools buyer’s guide. It’s designed to help engineering teams understand and navigate the challenges associated with shifting security into the development process, complete with a scorecard to grade tool options.